Protect Your Data: Best Practices for Data Security in Remote Work
Welcome to the world of remote work, where flexibility and freedom become the cornerstone of our professional lives. With the rise of remote work, companies and individuals alike are embracing the opportunities it brings. However, along with these opportunities comes the need to address an important aspect of remote work: data security.
As we transition from traditional office spaces to home-based workstations, ensuring the protection of our sensitive information has become paramount. Remote work poses unique challenges to data security, such as the risk of unauthorized access, data breaches, and cyber-attacks. Therefore, it is vital to be proactive and adopt best practices to safeguard your data.
The Complexity of Data Security
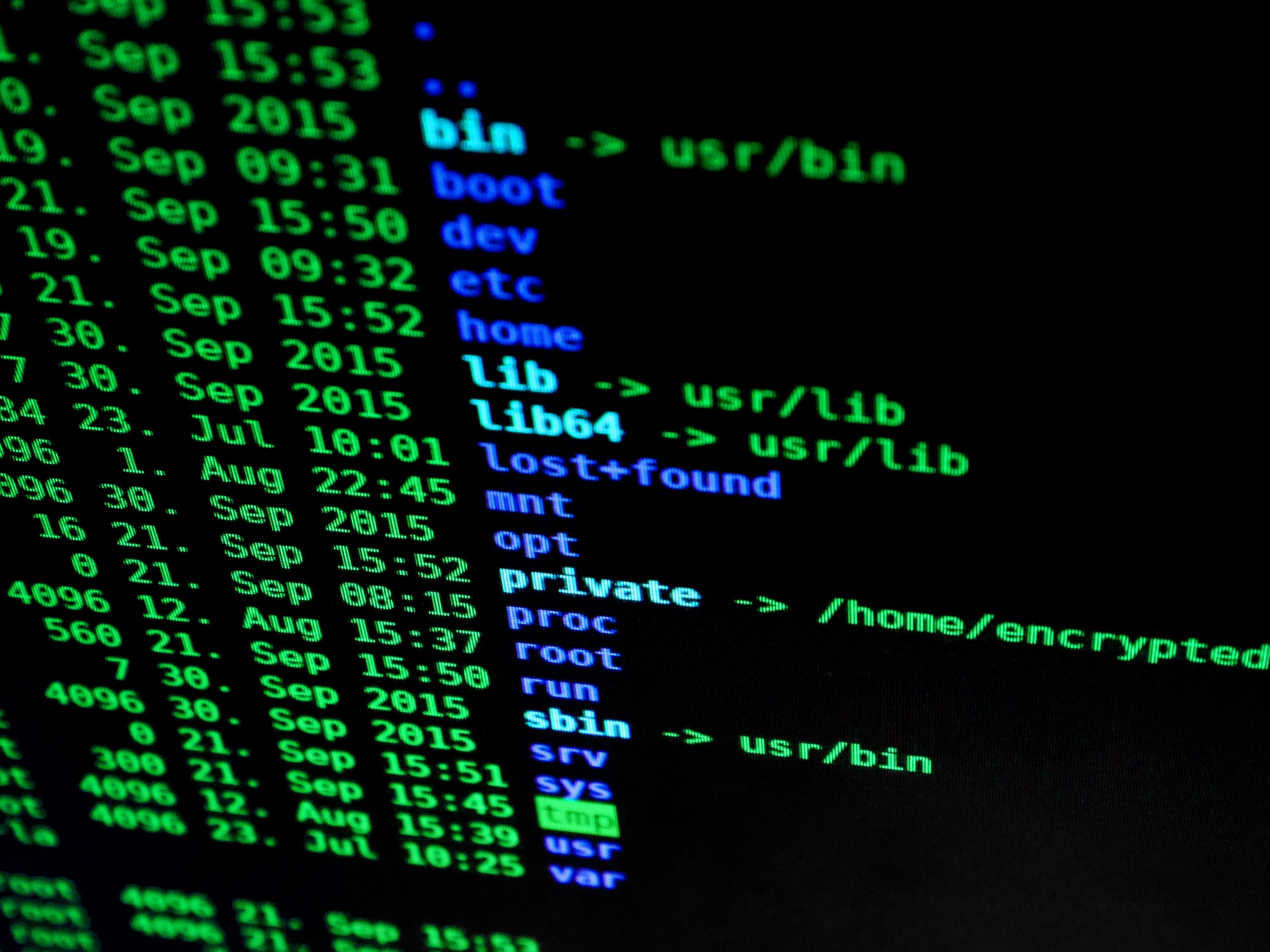
Data security in the remote work landscape can be complex due to the various devices, networks, and potential vulnerabilities present. The use of personal devices, unsecured public Wi-Fi networks, and potential gaps in knowledge among remote workers can significantly increase the risk of data breaches.
Embracing Burstiness in Data Security
Remote work environments tend to have a mix of diverse challenges and situations. This requires adopting burstiness, a concept which encourages the use of varying approaches, techniques, and tools to tackle data security issues effectively. It is essential to have a comprehensive security plan that covers encryption, strong passwords, two-factor authentication, and regular software updates.
Predictable? Not for Data Security!
While remote work offers flexibility, it also increases the unpredictability of potential security threats. Therefore, it is crucial to mitigate these risks and remain proactive. Regularly educate yourself and your team on the latest security best practices and technological advancements. Implement security measures that protect against phishing attacks, malware, and unauthorized access.
In this blog series, we will explore the best practices for maintaining stringent data security in a remote work setting. From securing your home network to establishing secure communication channels, we’ll provide you with practical tips, expert advice, and recommended tools to effectively protect your data.
Protecting your data is vital in today’s remote work landscape. Join us in our next post as we delve into securing your home network and creating a fortified digital boundary to safeguard your sensitive information. Together, let’s make remote work a secure and productive environment for everyone.

What are the Essential Steps for Ensuring Data Security in Remote Work?
In the realm of remote work, ensuring data security is of paramount importance. With increasing concerns about cyber threats and the vulnerability of remote work environments, it becomes crucial to implement the best practices for safeguarding sensitive information. This article aims to explore the essential steps and strategies that can help organizations and individuals protect their data while working remotely.
To begin with, establishing a robust and secure network infrastructure is fundamental. This includes using virtual private networks (VPNs) to encrypt data transmission and ensure secure connections. VPNs create a private and encrypted tunnel for remote workers to access company resources, minimizing the risk of interception or unauthorized access.
Another vital aspect of data security in remote work involves implementing stringent access controls. This entails using strong and unique passwords for all accounts and systems. Additionally, two-factor authentication (2FA) should be enabled wherever possible to add an extra layer of security. By implementing these measures, the risk of unauthorized individuals gaining access to sensitive information is significantly reduced.
Data encryption is another critical component of remote work data security. Encrypting sensitive data helps prevent unauthorized access even if the data is compromised. Therefore, it is essential to utilize encryption techniques to safeguard data both during transmission and at rest.
Regular data backup procedures are equally significant in data security for remote work. Ensuring that important files and documents are regularly backed up to secure and resilient storage systems minimizes the potential loss of critical information. In the event of a security breach or system failure, a reliable backup ensures data can be restored, reducing downtime and minimizing potential damage.
Lastly, comprehensive employee training and education play a crucial role in maintaining data security in remote work environments. Employees should be aware of the potential risks, such as phishing attacks or malicious software, and be equipped with the knowledge to identify and respond to these threats effectively. Regular training sessions and updates can help reinforce security protocols and ensure adherence to best practices.
This article has provided a concise overview of the essential steps for ensuring data security in remote work. Each topic discussed above will be further elaborated on in subsequent sections, delving into specific strategies and recommendations to establish a robust and secure remote work environment. Stay tuned for an in-depth exploration of each aspect, equipping you with the knowledge and tools to protect your data effectively.

Best Practices for Data Security in Remote Work
Remote work has become increasingly prevalent in today’s digital age, providing flexibility and convenience to employees. However, with the rise of remote work comes the need for robust data security practices to protect sensitive information. In this article, we delve into the best practices for data security in remote work, ensuring that your organization can maintain the integrity and confidentiality of its data.
Implement Strong Password Policies
One of the fundamental aspects of data security is the use of strong, unique passwords. Encourage employees to create complex passwords that include a combination of uppercase and lowercase letters, numbers, and symbols. Additionally, enforce regular password changes to minimize the risk of compromised credentials.
Statistic: According to a study by Verizon, weak or stolen passwords were responsible for 81% of hacking-related breaches.
Enable Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide additional identification factors, such as a unique code sent to their mobile device or a fingerprint scan, in addition to their password. By implementing MFA, you significantly reduce the chances of unauthorized access to sensitive data.
Encrypt Data and Communication Channels
Encrypting data and communication channels is essential to protect your organization’s confidential information from unauthorized individuals. Utilize encryption technologies such as Secure Socket Layer (SSL) or Transport Layer Security (TLS) to secure data transmission over networks. Additionally, encrypt sensitive files and folders stored on employee devices to prevent unauthorized access in case of theft or loss.
Regularly Update and Patch Software
Outdated software and unpatched vulnerabilities can pose significant risks to data security. Ensure that all employees regularly update their operating systems, applications, and security software to the latest versions. Promptly apply patches and security updates provided by software vendors to address any known vulnerabilities.
Utilize Virtual Private Networks (VPNs)
A VPN creates a secure connection between an employee’s device and the company’s network, encrypting all data transmitted between the two. By using VPNs, remote workers can securely access internal resources and protect their data from interception by unauthorized parties.
Train and Educate Employees on Security Awareness
Employees are often the weakest link in data security, unintentionally causing vulnerabilities through human error. Conduct regular training sessions to educate employees about the importance of data security, highlighting common threats such as phishing attacks, social engineering, and the risks of accessing sensitive data from unsecured networks.
Implement Access Controls and Least Privilege Principles
Granting employees access to only the data and systems necessary for their roles significantly reduces the risk of unauthorized data exposure. Implement access controls and adhere to the principle of least privilege, ensuring that employees have the minimum required permissions to perform their tasks effectively.
Monitor and Detect Anomalies
Implement robust monitoring systems to detect any anomalous activities or unauthorized access attempts. Utilize intrusion detection systems, log analysis tools, and behavior-based analytics to identify potential security breaches promptly.
- Regularly review system logs and security reports.
- Set up alerts for suspicious activities.
- Conduct regular security audits.
Conclusion
Data security in remote work is vital to ensure the confidentiality, integrity, and accessibility of your organization’s sensitive information. By implementing these best practices, including strong password policies, multi-factor authentication, encryption, software updates, VPNs, security awareness training, access controls, and monitoring, you can significantly enhance your remote work data security defenses, protecting your organization from data breaches and cyber threats.
Statistic: According to a survey conducted by the Ponemon Institute, 63% of businesses experienced a data breach as a result of a third-party vendor.
Conclusion
In conclusion, ensuring data security in remote work environments is of utmost importance for both individuals and organizations. By following the best practices outlined in this article, you can minimize the risks associated with data breaches and unauthorized access.
First and foremost, it is crucial to use strong and unique passwords for all your accounts and devices. Implementing multi-factor authentication provides an added layer of protection and reduces the likelihood of unauthorized access. Regularly updating your software and applications is equally important as it ensures that security vulnerabilities are promptly addressed.
Encrypting sensitive data and communication channels is another essential practice for remote work data security. Whether it’s through the use of virtual private networks (VPNs) or encrypted messaging services, encryption protects your data from being intercepted and compromised.
Additionally, educating yourself and your employees about the common methods used by cybercriminals, such as phishing and social engineering, can significantly reduce the risk of falling victim to these attacks. Being vigilant and cautious when sharing sensitive information or clicking on suspicious links is essential.
Implementing a robust backup strategy ensures that even in the event of data loss or ransomware attacks, your critical information remains intact. Regularly backing up your data to secure off-site locations or cloud storage services provides an extra layer of protection against potential disasters.
In conclusion, prioritizing data security in remote work environments requires a combination of technical measures, user awareness, and a proactive approach. By adhering to these best practices, you can safeguard your sensitive data and protect yourself from the ever-growing threats in the digital landscape.